This is the first part of a series on contested space. It presents the context and the threats facing today’s reconnaissance satellites. Part II presents potential countermeasures.
After the launch of the first satellites by the USA and the USSR, questions arose about the political status of space: was it to be subject to territorial claims, like land? Or was to be regulated as the open seas? War being the continuation of politics by other means, strategists of the time started to think about war in space: if a satellite is in orbit and threatens a country, how can it be taken down? In the context of the Cold War, these were not idle questions. The main uses of space turned out to be crossing intercontinental distances with nuclear weapons, and overflying hostile countries. So the international norms regarding space were of paramount importance.
These questions were partly settled by the USA and the USSR accepting to be overflown by each other’s reconnaissance satellites, and by the ratification of the Outer Space Treaty by those same countries. Under the treaty, they were and still are forbidden to make sovereignty claims on celestial bodies, and to place weapons of mass destruction in orbit. So for a time, the question of war in space was overshadowed by the more pressing threat of nuclear war on Earth.
However, over the years, the nature of space activities has evolved: from a strategic tool providing only long-term intelligence for planning, reconnaissance satellites have turned into a real-time, tactical asset, that can be integrated in conventional targeting loops. Space communications also enable to link not only a few commands posts, but now every asset across a theater, maximizing the effectiveness of each. Space acts as a force multiplier, especially in US armed forces, which rely on a large space component for reconnaissance, communication, and missile warning, in all of their operations.
Consequently, rivals of the USA have realized they need to eliminate this advantage if they are to win even a regional conventional conflict. China and Russia pursue counter-space capabilities, turning space from a relatively benign environment short of nuclear war, into a contested environment, like the traditional land, sea and air battlefields.
Their capabilities threaten not only the US space infrastructure, as explained by the US Director of the National Reconnaissance Office in the video below, or by the US Air Force Chief of Staff there, but also make conflict in space more likely for smaller space power such as France, whose Joint Commander for Space highlighted the vulnerability of his space assets at a recent hearing. Civilian experts have also noted this shift.
Keynote speech of the NRO Director, focusing heavily on the need to make her systems resilient against anti-satellite threats. A transcript is at the bottom of this article.
The case of reconnaissance
In the issue of contested space, reconnaissance satellites have a special place. Since most of them are close to Earth (in order to “see” better), they are the easier targets. They also have a great tactical utility, but their destruction is not the sign of a coming nuclear exchange in the way destroying missile warning or nuclear communication satellites would be. So attacking them is less likely to lead to a nuclear escalation, while it cripples the tactical intelligence available to the adversary. That makes them juicy targets.
Besides, a lot of things have to go right for reconnaissance satellites to produce useful results, and in a particular order: these steps are chained. So it is appropriate to speak of an intelligence chain for space reconnaissance. The chain is like this:
The situation on the ground is captured by a sensor carried on a satellite. The data is then transferred to a ground station, in some case through a data relay satellite. The ground station then sends the data somewhere it will be processed and analyzed, turning it into intelligence. Then, this intelligence product is disseminated to customers.
A nation seeking to deny the advantages of space reconnaissance to an adversary can attack any link in this chain, using one of the many ways listed below:
Controlling ground activity
The first, most obvious way to prevent a satellite from spying on a country is to avoid exposing suspicious objects and to suspend activities when the satellite is overhead. Because a low-orbit satellite can only look at a given site a few times a day at most, putting vehicles in hangars, closing missile silos and shutting down the radars are good ways to reduce the usefulness of space reconnaissance. It cannot be applied to everything, and short-term activity and mobile objects are easier to conceal than construction sites for instance. Another downside of this method is that if the adversary has a very high revisit rate, because it has many satellites or persistent satellites, then using it paralyzes the activity.
Conversely, one can choose to display activity when a satellite is present, to send a message: showing bombers being armed during a satellite pass is a good way to show determination.
Attacking the sensor
If changing the situation on the ground is not possible, because it would cause too much disruption for instance, then the next link to be attacked is the satellite’s sensor. It can be done in at least three ways:
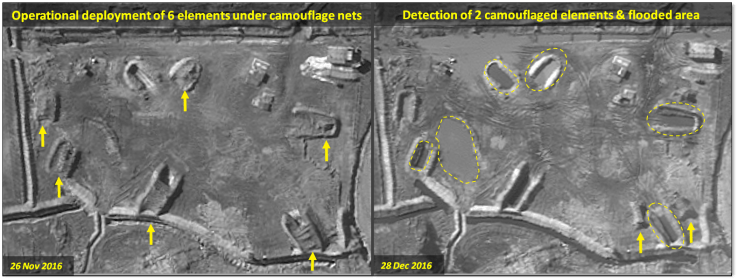
Camouflage
Camouflage is not a direct attack on the sensor, but it exploits the limitations of the sensor, by making the objects of interest undistinguishable from the terrain, or similar to other objects, so that the adversary cannot find them or cannot be sure what they are. Against optical sensors, camouflage nets are an interesting option, and are currently used by North Korea to hide the nature of the work being done on its submarines.
Decoys
Decoying has a long history, for instance the Allies used inflatable tanks during World War II to deceive German intelligence. Nowadays, the Russians, among others, have continued this tradition, and produce inflatable tanks, planes and missile launchers, to make the real version more survivable.
However, simple decoys may not fool modern sensors, or a combination of sensors: for a multispectral sensor to be confused, the decoy must have the same characteristics as the real thing in many wavelengths, for a thermal sensor it must have the same temperature, and for radar it must also be metallic to reflect radio waves. So a really accurate decoy has to be so similar to the true object that it may become complicated to deploy. Nevertheless, even a simple decoy may force the adversary to cue other sensors to investigate it, thus making them unavailable at other places where they would be needed.
Jamming
A more aggressive method is to jam the sensor. An optical sensor can be dazzled or saturated using a laser, something China has already used against US satellites. At higher power, laser can also damage sensor elements, making them permanently unusable. Because most optical satellites collect images through colour filters, either a wideband laser or several lasers are needed to jam all the wavelengths.
The size of the area denied by a laser depends on the power of the laser. A rough model (from The Physics of Space Security, section 11 Appendix A) gives that a 1kW laser can deny the imaging of an area 20 000 pixels wide.
A similar brute force approach can be used against radar sensors. Besides, due to the coherent nature of radar, more sophisticated techniques can be used, such as repeating the signal sent by the satellite, which is especially useful against synthetic aperture radar.
Attacking the Satellite
If the sensor is not vulnerable to attack, or if a more permanent solution is desired, attacking the satellite carrying it is a tempting option. Since it is not reversible, and it can create debris that endanger the satellites of third parties or of the attacker, it is a much more serious act. Several methods are available.
Direct ascent ASAT
This is the most energy-efficient method to physically destroy a satellite: a rocket is launched and reaches the altitude of the target satellite, and then either collides with it, or detonates a nuclear warhead. Since there is no need to match speed with the target before impact, the weapon does not need to be put in orbit first, so it is called a direct ascent Anti-SATellite (ASAT). Because most Low Earth Orbit (LEO) satellites have an altitude under 1000km, a relatively small rocket can be used.
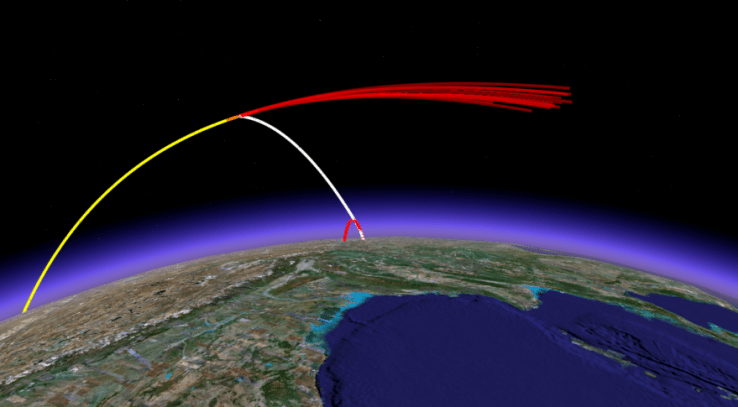
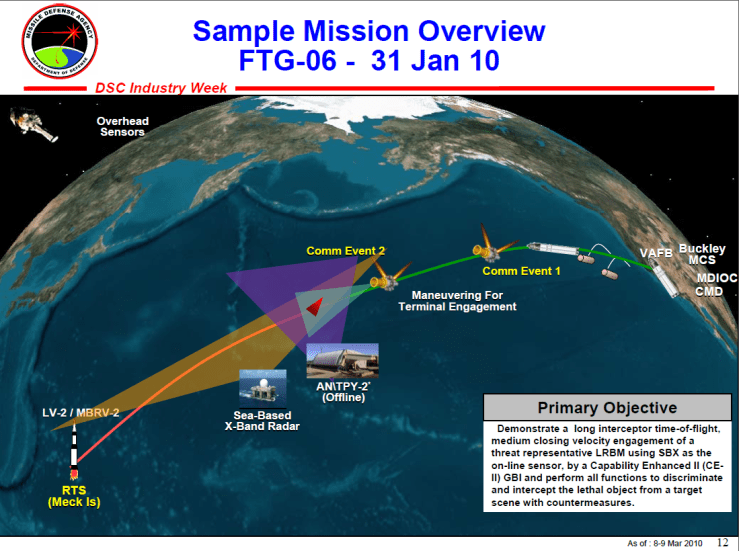
This kind of weapon dates back to the beginning of the space age: the USA conducted a test of an air-launched version, the Bold Orion, in 1959. Over the decades, several nuclear or conventional ASATs were deployed, such as the fighter-launched ASM-135. Nowadays, the United States do not officially have a deployed direct-ascent ASAT, but all mid-course interceptors used for anti-ballistic missile (ABM) defense inherently have anti-satellite capabilities: since they are able to hit ballistic warheads flying above the atmosphere, they can also hit LEO satellites. These systems include the GBI ground-based interceptors and the SM-3 ship-based missiles. The SM-3, in particular, demonstrated this capability in 2008, when it was used to shoot down a malfunctioning US satellite:
This was most likely a response to the 2007 Chinese ASAT test, in which China destroyed one of its own weather satellites, creating a significant number of debris in the process.
For conventional ASATs, which rely on the kinetic energy of the interceptor to destroy the target, the kill vehicle needs to maneuver very precisely to hit the target. Generally, the ABM kill vehicles have an IR sensor to detect the target and discriminate it from decoys, and a pulsed motor to zero in on it.

An evolved version carries multiple impactors, which decreases the effectiveness of decoys:
Higher orbits are also under the threat of direct-ascent ASATs, although bigger rockets are needed to reach higher altitudes: the Soviet developed the Naryad system to reach the Medium Earth Orbit (MEO), where the GPS satellites are located, and the Geostationary Earth Orbit (GEO), 36 000km up, where communications, missile warning and signal intelligence satellites abound.
China is also likely pursuing a high-altitude direct ascent ASAT. In 2013, it launched a rocket on a direct-ascent trajectory to a 10 000km altitude, allegedly for scientific purposes. However, US officials believe it was an ASAT test.
Co-orbital ASAT
The other method to hit a satellite is to put a weapon in a similar orbit, and then maneuver to get close. This requires a lot more energy that direct ascent, so a bigger rocket is needed. However, because the speed of the interceptor relative to the target is lower, there is more time to locate it and maneuver, so it can be easier to implement.
The Soviet developed an operational co-orbital ASAT capability, in the form of the Istrebitel Sputnik (satellite interceptor). These satellites were injected in almost the same orbit as their target, and then homed in on it using their onboard radar, before detonating a shrapnel charge when close enough. This took a few hours, compared the the few minutes required for a direct-ascent trajectory. The USSR tested the system many times, from the 1960s to the early 1980s.

Modern versions of the same concept exist. In 2015, a Russian satellite made headlines following its maneuvers that suggested a rendez-vous capability. Chinese satellites exhibited the same behaviour. The United States does it too, and for higher orbits: it launched the Prowler stealth satellite to inspect geostationary orbit, and has even officially acknowledged launching small inspector satellites, such as Mitex-A and -B, to the same orbit. Although they are not described as ASAT weapons, a small object impacting a fragile geostationary satellite is enough to put it out of service, so inspector satellites can be thought as undercover ASATs.
The kinetic ASAT do not operate alone: they are part of a “kill chain”, along with ground radars to detect, track and classify objects in orbit, potentially help guide the ASAT to its target, and assess the effects after the engagement. It is very similar to an ABM engagement, except that there is more time to prepare and the targets have a different signature.
Hacking
“Hard kill” is not the only concern for satellites. “Soft kill” solution exist. Apart from the jamming mentioned above, the satellites can also be hacked. An attacker gaining control of a satellite can then expend its propellant, send it in an uncontrollable spin, or shut it down temporarily or permanently in one way or the other. To prevent these attacks, command links to the satellite, and the telemetry it sends to the ground, can be encrypted.
This is not only a theoretical attack. In 2007 and 2008, Chinese hackers gained control of civilian US satellites, by hacking their ground station.
Attacking the Ground Segment
As seen in the hacking example above, the space segment -meaning the satellite itself- is not the only target for an attacker. A reconnaissance system always has a ground segment, consisting of radio antennas to receive the imagery and issue commands to the satellite, a processing center to turn raw pixels into exploitable products, an analysis center to derive intelligence from the imagery, and finally a communication network used to disseminate the intelligence. Usually, these systems are located in friendly territory, and in many case the distances involved make them hard to attack with conventional means. However, they can be soft targets: a large antenna cannot be buried in a bunker, so it is vulnerable to small munitions or even special force attacks. The end-user information dissemination network links many devices, and so is more vulnerable than a single ground station-satellite link.
A benefit of using kinetic attacks against the ground segment is that it does not create space debris, so third parties are not impacted. However, unlike satellites, these facilities can be manned, and so targeting them can cause casualties.
Conclusion
While anti-satellite capabilities are nothing new, technological advances and the heavy reliance of the US military on space assets have made them more relevant than ever, and have turned space into a potential battlefield. Consequently, most space powers look to increase the resilience of their systems. In the case of US reconnaissance satellite, the NRO’s policy seems to be to make their satellites defendable. How they can do that is the subject of the next article in this series.
Appendix: Excerpts of GEOINT 2016 Keynote by Betty J. Sapp, Director of the National Reconnaissance Office
(07:24) We still build [Hexagon-sized space systems] with our commercial industry partners. If you want to see very small targets and be able to characterize them, or if you want to hear very faint signals from hundreds or thousands of miles away from the Earth, you need big sensors. big sensors drive big systems. In fact if you want to combine sensitivity with persistence, you need even bigger systems with bigger sensors. So some missions still require those “Big bird”-type systems. But other targets demand a very different approach. Some missions for example, drive small, distributed systems flying low. We developed those systems as well. Yes, the NRO does small. i was asked a question recently at a forum like this one about why the NRO walked away from cubesats. The question made me smile. The questioner knew that NRO had been very very involved in the beginning of the cubesat, and wondered again why we had left them behind. My answer was that we had not left them behind at all. We used to use them just for technology and demonstration, and we launched them for others, but now we are using them for actual mission applications, which is why you don”t hear about it, because they are missions and cannot typically talk about in unclassified forums. So we build systems big and small, and every size inbetween, depending on what is required to do the mission. What also might surprise you is that we do more systems on the small end of that spectrum than on the large. […]
[…] (13:15) Imagine a ground architecture moving at machine speed, to notice the unusual hidden amongst the host of the usual. To anticipate the next move, not just react to the one just made. And to use all of our collection capability to best effect. If it sounds to good to be true or too complex to succeed, it’s not. Prototypes are driving operations today. Director Clapper talked about systems like Deep Blue, systems that were pitted against the best of humankind. We are talking about the successors to those systems, with far more at stake than the outcome of a chess game. [..] The magic really is on the ground, and we are counting on good engineering, not magic, to make it happen.
[…](19:40) We must be survivable, and we must be tactically responsive. We will be survivable. Like our partners in the Air Force, we are taking every measure to make sure we can survive the threats that are known, that we have seen demonstrated, and those we project. And we are practicing to capabilities, tactics and techniques in the JICSpOC, again with our Air Force partners. […]
Q & A
Q: You talked just then about the “explosion”, in your words, of threats to space assets. A short time ago I interviewed General William Shelton, former director of Space Command, and he said it’s his impression that this is a space war the US is losing, that it’s falling behind threats particularly from China but also Russia. […] I wondered if you dispute this characterization […]
Answer from NRO director Sapp: I think we were slow to recognize the change, I think we’ve been very good at catching up. So you’ve got what you’ve got in space, you can’t react immediately, we we’ve got new techniques, tactics, procedures to make sure we can react to the threats we’ve seen demonstrated. And we’ve got lots of plans for the future, and the future starts measuring next year, to make sure that we can take on all the threats that we project. So we will be survivable, and I think the adversaries recognize the importance of space to the US […].
Q: There’s a lot of talk over an overdependence on space assets [] our enemies know of that dependence, and therefore of course are developping weapons to target them. Is there over dependence in your view? Have we become so enthralled by technology that if those assets were ever lost, or damaged, or threatened, would the US military be crippled?
A: (27:56)I think the US military would definitely be at a disadvantage. I’m not sure I’d ever say we are overly dependent on space, in fact I’d like them to be more dependent on space. But we have to make sure it’s survivable. The US does not have and cannot afford the kind of numbers that you’d have to make up, in either people or weapons systems, to make up for the space advantage. [] Space is a real multiplier [] the military did some “days without space” and it was ugly. They did not want to go back there, and we’ve felt the same questions asked from some of our foreign partners. We can’t afford the alternative, so we have to make sure that we are making space survivable,and it’s gonna do what the military and what the policymakers are counting on.
[]
(29:14) There’s a lot of debate about big systems, especially when we talk resilience. Are big systems more vulnerable that smaller proliferated systems? And our answer was no, in fact we have done a lot of studies. For small systems you’ve got bigger numbers but they are not that hard to target, and they can’t protect themselves usually. So that’s one answer. The other answer is you want resilience but you want to actually have a mission capability. Having something up that’s extremely survivable but doesn’t do the job is not very helpful. Having something up that’s really optimized for the job but that’s not survivable isn’t very helpful either. So we need to find that balance between. And again, I’ll point out, sometimes you need a big front end for it to do the job it needs [to do]. And you can’t put a big front end on a very small system. So again, finding that balance between what it needs to the mission and making sure that mission capability is very resilient no matter what the threat, that’s a job we’re trying to do today.
Q:(36:52) Can I ask you just to characterize the threat today to space assets and who is your greatest concern?
A: We have threats we’ve seen, we have certainly seen lasers and jammers, we have seen those demonstrated not just by China and Russia but by others, you can buy jammers on the internet. So we known we have those to worry about. We certainly saw the Chinese demonstrate their direct ascent weapon in 2007 and we’ve seen plan for many many other things. So we worry most about the Chinese and the Russians.I’d be a hard call to say who amongst those two we’re most worried about, we’re worried about both, and their systems and capabilities are different. So we have to plan against both. We’ve atrophied a little bit in our ability to not only understand the threat but also react to those threats. We’ve lived in a very benign environment in space for a while. So we have not had so much threat since the Soviet Union days. So retraining and relearning those skills is what we’re very focused on. If something happens to a satellite in space, its operators tend to look at it like “well this space system is misbehaving, it’s an anomaly” and maybe we need to consider “maybe somebody’s doing something to me”. That’s not a question that my operators ask today, or rather it’s not a question they used to ask. They do ask it today. So we need to retrain people, and certainly we need different training than what we have ever given our operators and our system developers. And we are working on that, in partnership with StratCom, the Air Force and everybody else that’s in this fight with us.
Q: You mentioned the Chinese launch in 2007, the follow-on, this Russian launch with the “rocket stage that came alive”: the maneuverable satellite, people use the term kamikaze satellite. How advanced is that technology today, how much of a threat?
A: We worry about direct ascent weapons, we worry ever more about things that are already in space, because the timelines are different. So we worry about all of it, and again, we are taking measures against all of it. We understand the timelines, we understand what we have to do.
Q: What’s your biggest challenge? What keeps you up at night?
A: (42:00) It is making sure we are going to be resilient. We are very very focused on that but we can’t know what we don’t know. We want to make sure we understand all the threats that might come against us, the timelines they are on, and make sure we are ahead of that timeline. So if there is something that gives me pause, it’s that. making sure that we are going to be ready.
Q: Just a little follow-up on that. In the cyber realm, I often hear about cyber experts inside and outside government that they are concerned and very much aware of the threat, they know where it is coming from, they have a sense of what to do, they will often complain that that sense of urgency is not matched by some of their civilian counterparts – the folks who are writing the checks- and I’m curious: is that the same on this threat to you? Do you get the support you need, do you think that folks in Washington understand? .
A: Yes, I really do. if there is something that has got White House attention and leadership attention throughout the Pentagon, it has been resilience in space. As we have stood up the JICSpOCnow, we have had SecDef, Dep SecDef, national Security Adviser, we have had a host of visitor that have showed the kind of interest required to travel out and see that. And they have not just touched base with it, they have stayed for hours and understood what we were doing and how far we had to go. You can tell it is a priority when the money actually follows, and for this kind of budget environment, for us to spend literally billions on both sides of the IC side and the DoD side to afford additional resilience, the huge, huge investment is a sign that it is a huge priority for the US.




[…] previous article in this series was a reviews of the many threats a reconnaissance satellite faces. It opened with an interview of […]
LikeLike
Reblogged this on The restless technophile.
LikeLike
[…] find the minister’s assessment of the threats and the means she proposes to counter them echo previous articles on contested space. Notably, she alluded to the idea of France developing her own ASAT […]
LikeLike
[…] So in all likelihood, the US answer would consist in something akin to the initial plan for STSS, a constellation of satellites in low Earth orbit with below-the-horizon sensors. Depending on their orbit, they could also pull double-duty as warhead tracking satellites if their are equipped with an above-the horizon sensor optimized for cold targets too. Having a constellation with a relatively large number of satellites would be consistent with the US push for disaggregating their space segment to be more resilient to counterspace threats. […]
LikeLike
[…] more background on the threats satellites face, see Contested Space I: Threats , and for possible ways to counter them see Contested space II: Countermeasures […]
LikeLike
[…] Other options to counter satellites exist, but they are lot more aggressive and can cause debris problems. […]
LikeLike
[…] military advantage to the USA. The best shot their adversaries might have is to field a soft-kill anti-satellite system, to avoid creating debris and not spend more money per shot that the target is […]
LikeLike
[…] Thus, putting many cheap platforms on orbit allows for a more graceful degradation in case of an anti-satellite attack. Whereas losing one satellite in a system of two very expensive platforms is a huge blow, losing […]
LikeLike
[…] even revealed the name of the weapon development program: FLAMHE. The use of a laser instead of a kinetic impactor comes from the fact that France has forbidden itself from creating dangerous debris that could […]
LikeLike